As a Linux administrator with a decade of experience managing Linux servers, I can shed some light on the idea that Linux systems are immune to viruses and malware.
While it’s true that Linux is less prone to these threats compared to other operating systems like Windows, it’s not entirely immune. The main reason behind this perception is the way Linux is built—it’s based on a robust architecture with strong security measures in place.
However, Linux systems can still be vulnerable if not properly maintained and secured. Just like any other operating system, Linux can fall victim to security breaches if users don’t update their software, use weak passwords, or download and install software from untrusted sources.
In this article, we’ll delve into the reality of Linux security and discuss the steps Linux administrators can take to mitigate the risks of viruses and malware.
We’ll explore best practices for maintaining a secure Linux environment, including regular software updates, implementing strong authentication mechanisms, and employing security tools like firewalls and antivirus software.
By understanding the truth about Linux security, we can better protect our systems from potential threats.
Is Linux Operating System Immune to Malware
Let’s be honest, no operating system is completely safe from viruses and malware, but Linux doesn’t seem to get hit by them as often as Windows. Why is that?
Some folks think it’s because Linux isn’t used as much, so hackers don’t bother making malware for it. They figure it’s not worth their time. But if that were true, Linux servers would be a big target, since so many important systems (companies) run on Linux.
But even though Linux is everywhere, it’s not as easy to break into. It’s built strong, making it tough for viruses to take hold. And there are lots of different versions of Linux out there, all based on the same core, which adds extra layers of security.
So, while Linux isn’t bulletproof, its design and diversity make it a harder target for hackers.
System-Specific Malware: RPM vs. Debian-Based Systems
Imagine someone creating a harmful program for a RedHat, Fedora, or CentOS system, which won’t affect a Debian-based system like Ubuntu. Similarly, a harmful program for Debian won’t harm a RedHat-based system.
- How to build a website with WordPress and what are the best plugins to use: WordPress Web Design Tutorials: How to build a website with WordPress and what are the best plugins to use. Building a website with WordPress is an excellent choice due to its versatility, ease of use, and a vast array of plugins that enhance functionality. Here’s a comprehensive guide to building a WordPress website, along with recommendations for the best plugins.
- The Most Important Stages and Plugins for WordPress Website Development: Developing a WordPress website requires careful planning, execution, and optimisation to ensure it is functional, user-friendly, and effective. The process can be broken into key stages, and each stage benefits from specific plugins to enhance functionality and performance. Here’s a detailed guide to the most important stages of WordPress website development and the essential plugins for each stage.
- What are the most powerful Tools for SEO in WordPress?: Powerful SEO Tools for WordPress: Search Engine Optimisation (SEO) is essential for improving your WordPress website’s visibility in search engines. Here are the most powerful tools to optimise your site effectively:
- How to add shipping modules in CubeCart: Step 1: Log in to Your CubeCart Admin Panel: Open your web browser and navigate to your CubeCart admin login page. Enter your username and password to log in.
Step 2: Navigate to the Extensions Section: Once logged in, go to the left-hand menu and click on Manage Extensions. From the dropdown, select Extensions.
Step 3: Find Shipping Modules: In the Extensions section, locate the Shipping tab to view available shipping modules. You can browse through the list or use the search function to find a specific module. - Gathering domain and IP information with Whois and Dig: In the digital age, understanding the intricacies of domain and IP information is essential for anyone navigating the online landscape. This article explores two powerful tools—WHOIS and DIG—that help gather valuable insights about websites and their underlying infrastructure. Whether you’re a cybersecurity professional, a web developer, or simply curious about online resources, you will learn how to effectively utilize these tools, interpret their outputs, and apply this knowledge to real-world scenarios.
- What are the best WordPress Security plugins and how to set them up the best way: Read a comprehensive guide on the best WordPress security plugins and how to set them up to ensure optimal protection for your WordPress site.
- Will a headland provide enough shelter?
- Learn How To Purchase Your Own Domain Name with Fastdot.com: Open your web browser and go to Fastdot.com. Navigate to the Domains section, either from the homepage or from the main navigation bar.
Step 2: Search for Your Desired Domain Name: In the domain search bar, type the domain name you want to purchase. Fastdot supports a wide range of domain extensions (TLDs), such as .com, .net, .org, .com.au, and many others. Click the Search Domain button. The system will check the availability of your desired domain name.
Also, if a program wants to make big changes to the system, it needs the root password. If that password is strong and kept secret, the system stays safe.
A virus made for Windows won’t harm Linux unless you install Wine and run it with root privileges. That’s why it’s advised not to run Wine as root.
Password Setup and User Permissions in Linux vs. Windows
In Linux, you need to set up both a root password and a user password. Every user, except ‘Guest‘ must have a password. But in Windows, you can set up user and root accounts without passwords.
In Linux, you can’t run programs, like installing or uninstalling, without permission (using ‘sudo‘ or root password). However, in Windows, programs can be installed or uninstalled without root consent.
You can run Linux without a graphical interface (GUI), but you can’t do the same with Windows. Many System Administrators disable GUI in Linux for security reasons, yet it remains productive.
Understanding Linux Security
Linux is designed with strong security features, making it safe even without a firewall when not connected to a network. One of these security measures is called Security-Enhanced Linux (SELinux), which includes special tools and changes to the core of the system to enforce security policies.
While SELinux isn’t necessary for regular users who aren’t connected to a network, it becomes crucial for those who are, such as network users and administrators.
Think of SELinux as a guard that watches over your system, ensuring only authorized actions are allowed. It’s like having a set of rules that dictate what can and cannot be done on your computer. When connected to a network, the risks of unauthorized access and attacks increase, so SELinux helps to protect against these threats.
For everyday users who don’t connect to networks often, SELinux might not be something they need to worry about. But for those who manage networks or regularly access them, SELinux provides an extra layer of security, helping to keep sensitive information safe from potential breaches.
You can get a free antivirus called ‘Clam AV‘ for your computer, which is open source, meaning anyone can use and modify it.
If your computer is connected to a network, it’s a good idea to install it to protect your computer from viruses and other harmful software, giving you more security.
Besides these measures, you can encrypt your disk, set a boot loader password, create custom boot settings, and define user roles, making Linux very secure. However, Linux systems still face certain threats, which we’ll discuss here.
Notable Linux Security Incidents
Several notable security incidents have highlighted Linux’s vulnerability to cyber attacks:
- Shellshock (CVE-2014-6271) – In 2014, a critical vulnerability in the Bash shell, known as Shellshock, exposed millions of Linux and Unix-based systems to remote code execution attacks.
- Dirty COW (CVE-2016-5195) – The Dirty COW vulnerability, discovered in 2016, allowed attackers to exploit a race condition in the Linux kernel’s copy-on-write mechanism to gain root privileges on vulnerable systems.
- Cryptomining Malware – Linux-based servers have become prime targets for cryptomining malware, which hijacks system resources to mine cryptocurrencies without the user’s consent.
Strengthening Linux Security Practices
To enhance Linux’s resilience against malware and security threats, users and administrators can implement the following best practices:
- Regular Updates and Patching – Stay vigilant about installing security updates and patches for the Linux kernel, system libraries, and installed software packages to mitigate known vulnerabilities and security flaws.
- Hardening and Configuration – Implement security hardening measures, such as disabling unnecessary services, enabling firewalls, and configuring access controls to minimize attack surfaces and fortify system defenses.
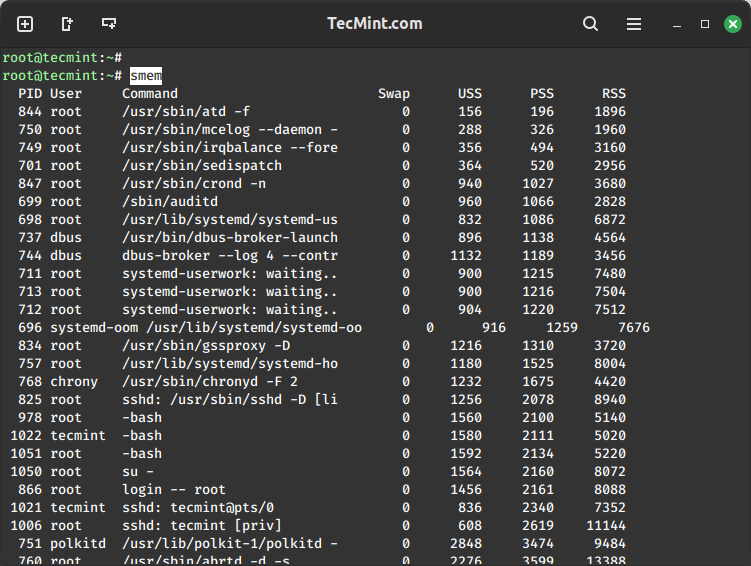
- Monitoring and Logging – Monitor system logs and network traffic for signs of suspicious activity, intrusion attempts, or unauthorized access.
- Install IDS – Implement intrusion detection systems (IDS) and security information and event management (SIEM) solutions to enhance threat detection capabilities.
- Security Awareness Training – Educate users and administrators about security best practices, phishing awareness, and safe computing habits to reduce the risk of social engineering attacks and inadvertent security breaches.
Conclusion
In summary, although Linux is known for being secure, it’s not completely safe from viruses and malware. The belief that Linux is virus-free comes from its strong security features, open-source nature, and fewer desktop users compared to Windows.
Still, Linux can be targeted by cyber attacks, human mistakes, and security flaws. By taking proactive security steps, staying informed about new threats, and practicing good online habits, users and admins can reduce the risks and protect Linux systems.
While Linux isn’t totally free of viruses, it remains a reliable and secure system with careful security measures and risk management.