How to Schedule a Linux Job Without Cron
The post How to Schedule a Linux Job Without Cron first appeared on Tecmint: Linux Howtos, Tutorials & Guides . The world of Linux is filled with so much fun and interesting stuff, the more…

The post How to Schedule a Linux Job Without Cron first appeared on Tecmint: Linux Howtos, Tutorials & Guides . The world of Linux is filled with so much fun and interesting stuff, the more…
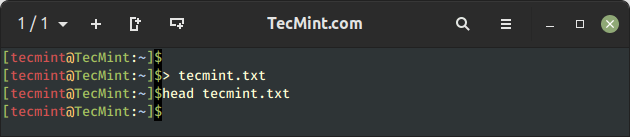
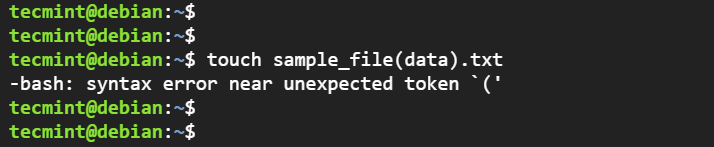
Files are one of the most important objects of any operating system and Linux is not an exception. Files provide a reliable way of storing data in a persistent manner. Linux uses plain text files…
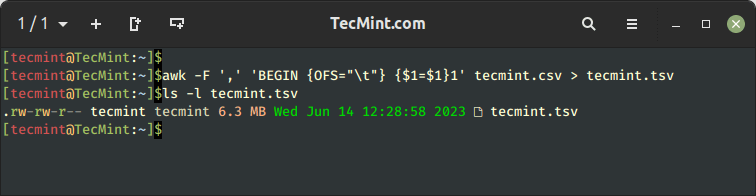
When it comes to managing and analyzing data, converting files from one format to another is a frequent need. If you are working with CSV (Comma-Separated Values) files in Linux and want to convert them…
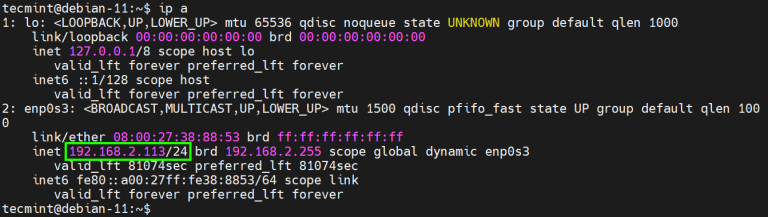
As a systems administrator, you will occasionally be tasked with configuring or setting up the IP addresses of your servers to keep up with changing network requirements. As such, having fundamental skills in assigning IP…
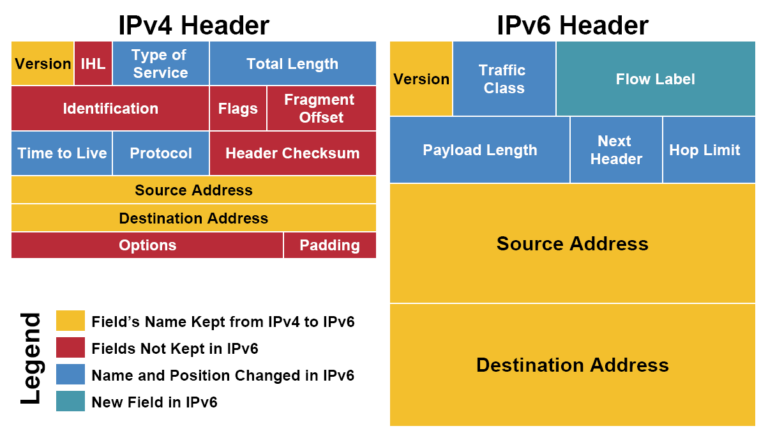
For the past 10 years or so, this has been the year that IPv6 will become widespread. It hasn’t happened yet. Consequently, there is little widespread knowledge of what IPv6 is, how to use it,…
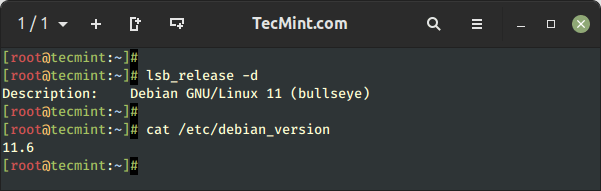
Are you planning to upgrade to the latest release of Debian 12 (codenamed “Bookworm”), from Debian 11? But did you know that instead of downloading the Debian 12 ISO file and installing it, you can…
The ‘!’ symbol or operator in Linux can be used as a Logical Negation operator as well as to fetch commands from history with tweaks or to run previously executed commands with modification. Most of…
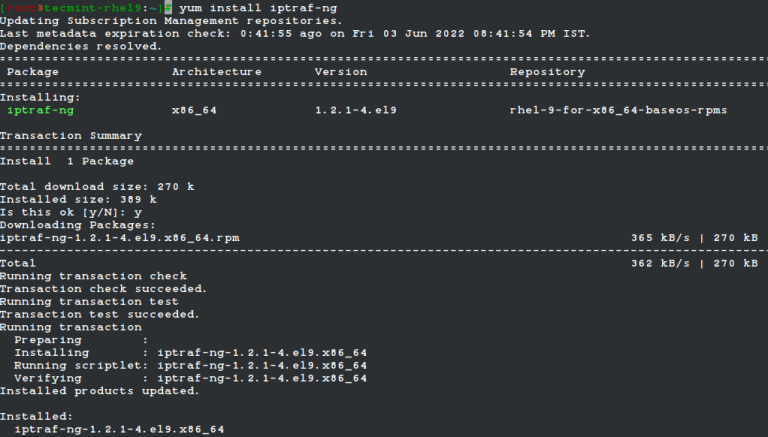
IPTraf-ng is a console-based Linux network statistics monitoring program that shows information about IP traffic, which includes information such as: Current TCP connections UDP, ICMP, OSPF, and other types of IP packets Packet and byte…
![How to Use the Cat Command in Linux [22 Useful Examples]](https://hostingmate.net/wp-content/uploads/2023/06/how-to-use-the-cat-command-in-linux-22-useful-examples-768x336.png)
The cat (short for “concatenate“) command is one of the most frequently used commands in Linux that comes pre-installed in most Linux distribution systems and is primarily used to display the content of existing files….
Exploiting a zero-day vulnerability in MOVEit Transfer, criminals have deployed web shells on vulnerable file transfer servers and gained access to a variety of high-profile organizations. More than a week since remediation instructions were published,…
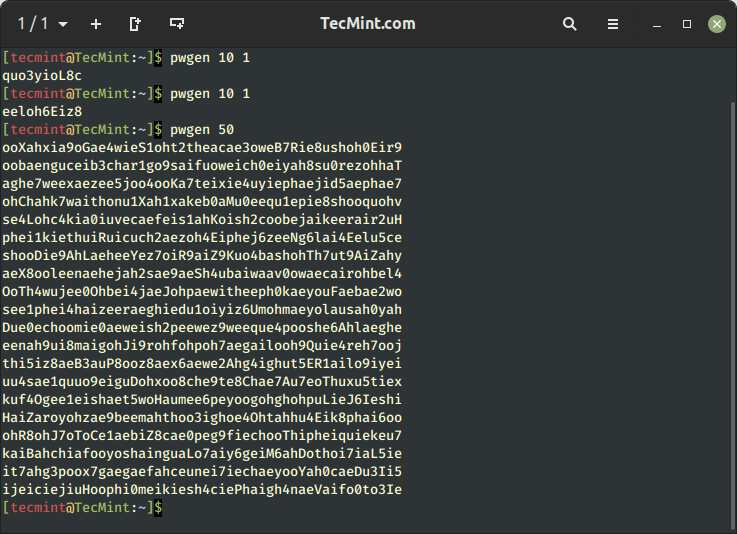
In this article, we will share some interesting command-line tools to generate random passwords and also how to encrypt and decrypt passwords with or without the slat (a security measure used in password hashing) method….

While using the command line, you can directly pass the output of one program (for example a tool that generates some system information or statistics) as input for another program (such as text-filtering or pattern-searching…

In this guide, we shall bring to light a simple yet important concept in process handling in a Linux system, which is how to completely detach a process from its controlling terminal. When a Linux…

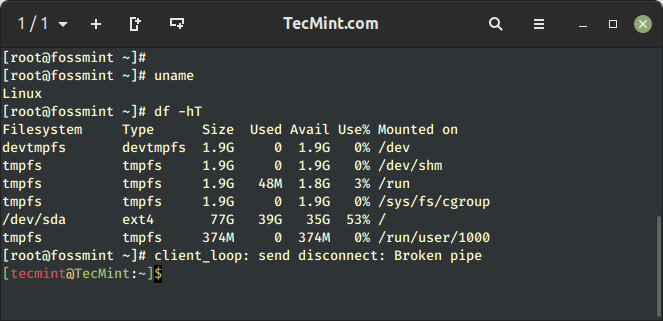
The post 10 Commands to Collect System and Hardware Info in Linux first appeared on Tecmint: Linux Howtos, Tutorials & Guides . It is always a good practice to know the hardware components of your…

The post 15 Useful Performance and Network Monitoring Tools for Linux first appeared on Tecmint: Linux Howtos, Tutorials & Guides . If you’re working as a Linux/Unix system administrator, sure you know that you must…

The post 16 Best Tools to Access Remote Linux Desktop first appeared on Tecmint: Linux Howtos, Tutorials & Guides . Accessing a remote Linux desktop computer is made possible by the remote desktop protocol (RDP),…

The post 11 Best IP Address Management Tools for Linux Network first appeared on Tecmint: Linux Howtos, Tutorials & Guides . If you are a network administrator, you surely know, how important it is to…

Are you having problems monitoring your Linux network bandwidth usage? Do you need help? It’s important that you are able to visualize what is happening in your network in order to understand and resolve whatever…
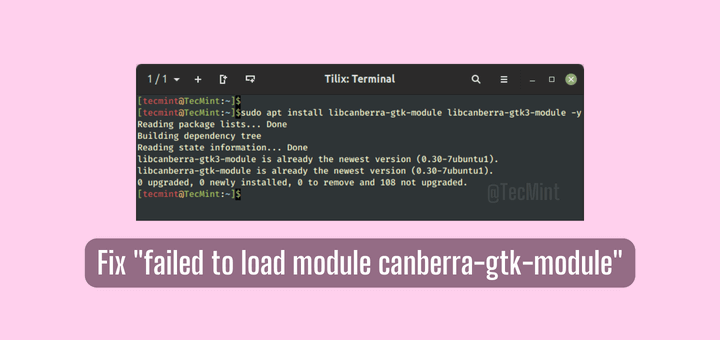
GTK, an abbreviation for GNOME Toolkit, is an open-source and feature-rich development toolkit used for creating GUI applications. It’s free and open-source and offers a rich set of UI tools for creating stunning and immersive…

A port is a logical entity that represents an endpoint of communication and is associated with a given process or service in an operating system. In previous articles, we explained how to find out the…
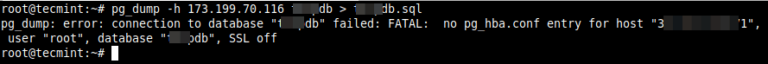
In a production environment, no matter how large or small your PostgreSQL database may be, regular backup is an essential aspect of database management. In this article, you will learn how to backup and restore…
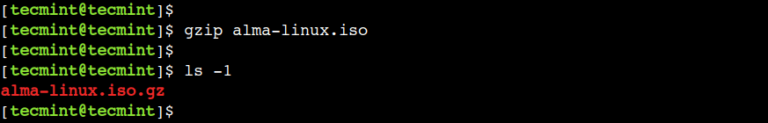
Compression is a very commonly performed operation by users to save disk space as well as reduce time and bandwidth while transferring large amounts of data over the network using gzip utility. gzip stands for…
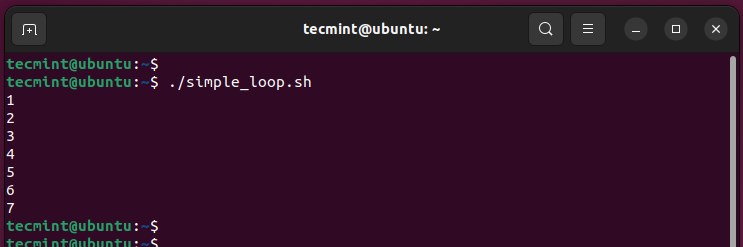
In programming languages, Loops are essential components and are used when you want to repeat code over and over again until a specified condition is met. In Bash scripting, loops play much the same role…
Bash (Bourne Again Shell) is a command-line program that accepts commands provided and executes them. It takes Linux commands directly typed into it interactively from a keyboard or from a shell script file. Bash is…
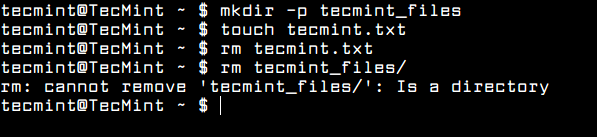
The rm command is a UNIX and Linux command line utility for removing files or directories on a Linux system. In this article, we will clearly explain what actually rm and “rm -rf” commands can…
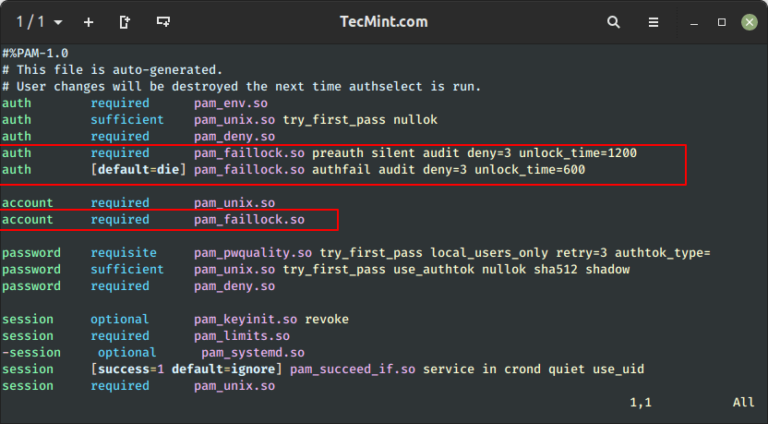
In Unix/Linux systems, the root user account is the super user account, and it can therefore be used to do anything and everything achievable on the system. However, this can be very dangerous in so…
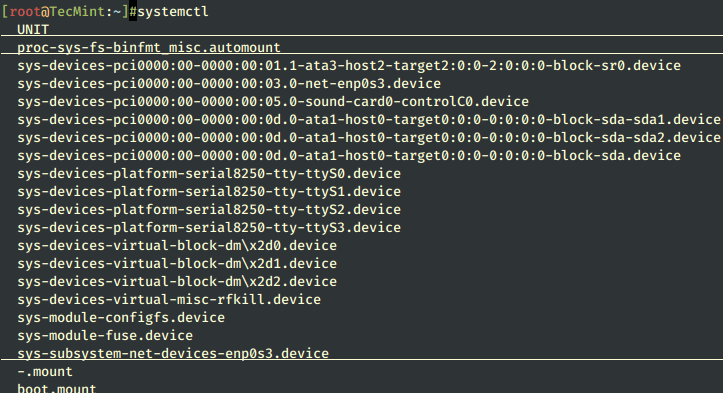
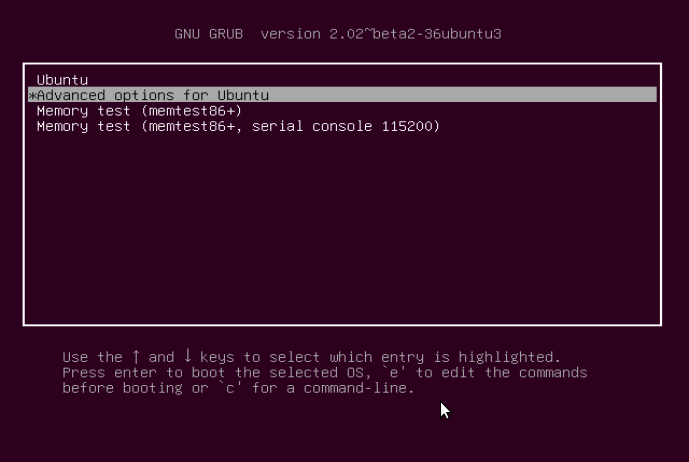
Linux systems provide a variety of system services (such as process management, login, syslog, cron, etc.) and network services (such as remote login, e-mail, printers, web hosting, data storage, file transfer, domain name resolution (using…
SSH security is a top priority when setting up your server. The default SSH settings are usually not robust enough to safeguard your server from external attacks. Therefore, additional tweaks are needed to provide a…
SSH, an acronym for Secure Shell, is a remote network protocol that is used to securely connect to remote devices such as servers and network devices over a TCP/IP network. It is a cryptographic network…
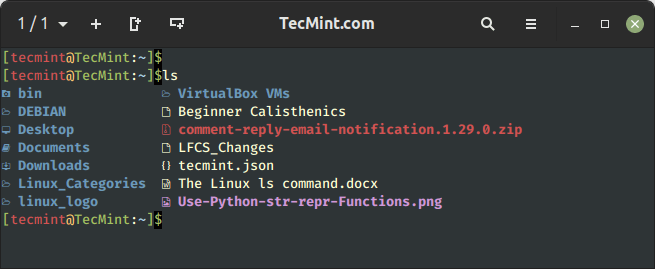
Listing files is one of the most widely undertaken tasks by ordinary Linux users and system administrators. In Linux, the ls command, short for “list” is used to list or display the contents of a…
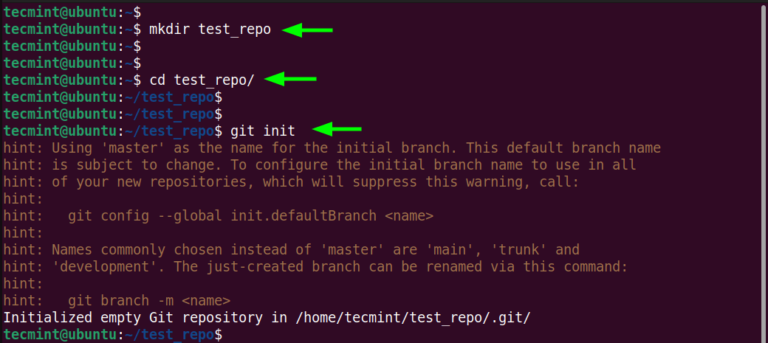
Git is the most popular version control system (VCS) used by developers and development teams to keep track of changes made to source code. In fact, it is the most popular version control system used…
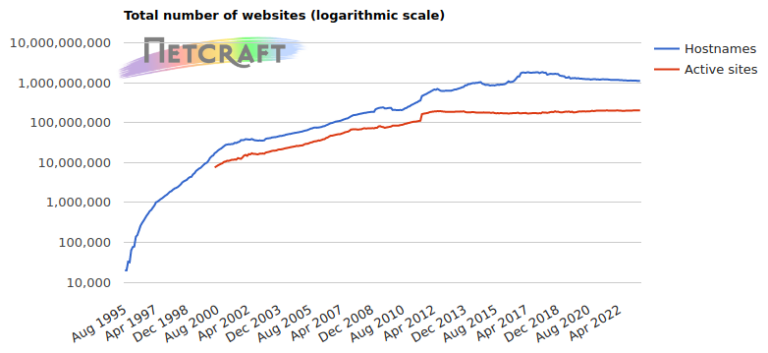
In the May 2023 survey we received responses from 1,109,384,426 sites across 271,534,718 domains and 12,037,194 web-facing computers. This reflects a loss of 6.0 million sites, 976,941 domains, and 52,213 web-facing computers. Microsoft saw the…
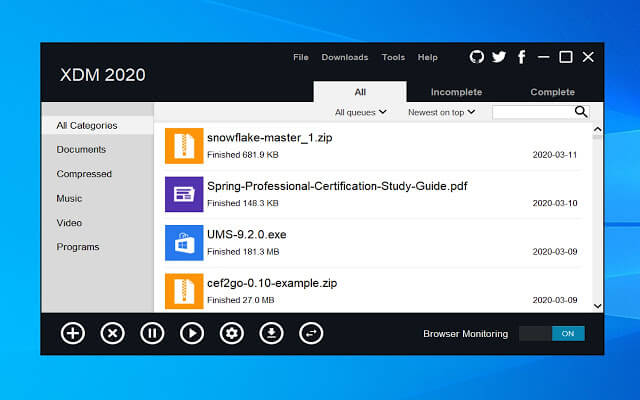
Download managers on Windows are one of the most needed tools that are missed by every newcomer to the Linux world, programs like Internet Download Manager Download Accelerator Plus and Free Download Manager are very…